Why I Trust (and Tweak) My Solana Wallet: A Browser Extension Guide
Whoa! I keep coming back to this topic. My instinct said a browser extension wallet had too many tradeoffs at first, but then I dug in and changed my mind. Hmm… some of that was personal bias—I’m picky about UX—and some of it was real, practical wins that made managing Solana actually easier for everyday use.
Here’s the thing. Browser extensions are conveniently right there while you browse NFTs, DeFi dashboards, and dapps. They pop up, ask for permission, sign a transaction, and vanish. Really? Yes, and no. The convenience is huge, but convenience carries risk; you have to be deliberate about how you set things up and what you approve. Initially I thought one-click approval was fine, but then I watched a suspicious dapp drain a test wallet and that changed my approach.
Short thread: set boundaries. Use separate accounts. Keep a show-stopper recovery plan. Okay, I’ll unpack that.
Why a browser extension for Solana?
Extensions give fast access to on-chain features without running a full node or juggling CLI tools. They’re great when you’re zipping between markets or minting drops at 10:02 AM. But speed means you must think faster about permissions. Seriously? Yep. Your extension holds signing power. That’s not just a phrase. It means any site that convinces you can move tokens, and your instinct matters a lot here.
So how do you balance ease and safety? First: compartmentalize. I use three wallets. One for gas and small trades, one for mid-level activity, and one cold wallet that stays untouched except for big moves. On the one hand it’s a wee bit annoying to hop wallets. On the other hand I sleep easier.
Something felt off about giving every new site blanket permissions. My advice: deny by default. Treat permissions like a faucet you control. If a dapp genuinely needs a particular permission, you can grant it. If it doesn’t, walk away. Oh, and keep receipts—screenshots of approvals—sometimes those little traces help during disputes.
Choosing an extension: trust signals and red flags
Look for audited code, active maintainers, and community chatter. An open source project with transparent commits is usually better than a closed binary you can’t inspect. Still, audits matter but they’re not ironclad. Audits reduce risk, they don’t remove it.
Red flags: unknown developer domains, weird permission requests that ask for “all accounts” or “unlimited transfer.” Also watch out for fake clones. There are lookalike extensions that mimic popular wallets. When in doubt, go to the official site or the app store listing. When I first installed a wallet, I double-checked the publisher name in the Chrome Web Store and then cross-checked GitHub activity—two quick checks that caught a suspicious copy once.
If you want to try a mainstream option, consider the Phantom experience—it’s polished and widely used. You can find the official download page for the phantom wallet here: phantom wallet. That link goes straight to the extension landing page I used when onboarding a new device.
Setup checklist (what I do, step-by-step)
First: fresh install on a trusted machine. I avoid installing on public or borrowed computers. Simple, yes, but very very important. Next: create a new wallet and write the seed phrase down on paper. Do not store it in plain text on your laptop. Seriously—don’t. I once saw someone sync their seed to cloud notes and then lock their keys behind a weak password. Not smart.
Then enable a hardware wallet if you can. It’s a pain to configure, and sometimes UX is rough, though actually the security payoff is worth it. On Solana, you can pair hardware wallets for signing higher-value transactions, which keeps everyday browser-level approvals limited to small ops.
Limit the number of active accounts in the extension. Having three accounts inside a single extension can be convenient, but it increases blast radius if the extension is compromised. I prefer a single working account for daily activity and a separate cold account on a hardware device.
Approving transactions: a practical rulebook
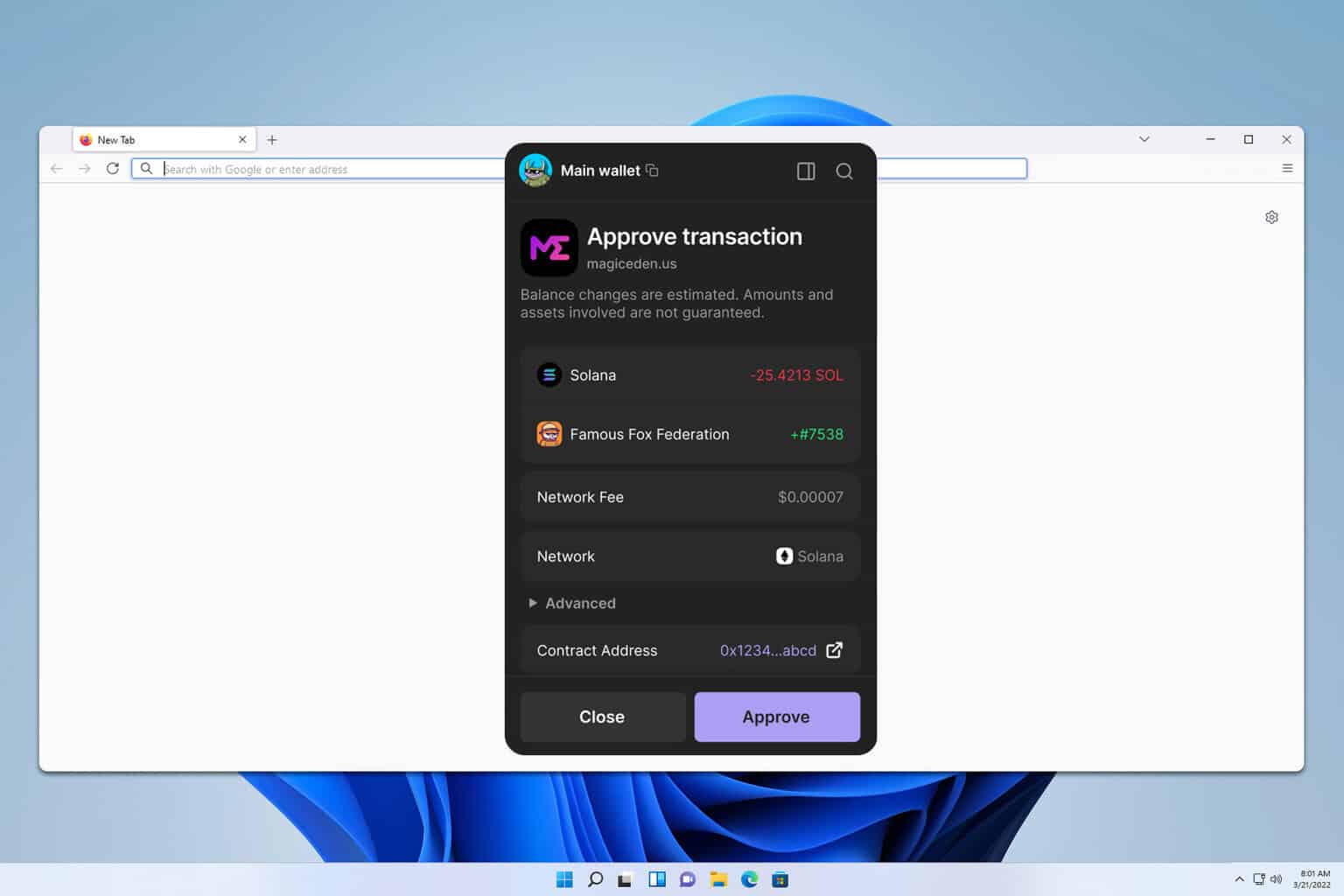
Read the payload. Yes, it can be annoying. But read the request, check amounts, and confirm the destination address if the UI exposes it. If a dapp asks to “sign something” and the text is opaque, back out. I’ve done this more than once—paused, unchecked a box, and then re-evaluated after checking the contract on a block explorer.
Also, keep gas limits and token approvals in mind. Some approvals set allowances that persist. Don’t set unlimited approvals unless you absolutely trust the dapp. If you’re not sure, set a small allowance or deny entirely. The small annoyances save you from headaches later.
Oh, and if a popup appears out of nowhere, don’t immediately click accept—take a breath. Your gut is sometimes right. I’ve had moments where my first instinct said “nope” and later that instinct saved a wallet.
Troubleshooting quirks
Extensions can be finicky with browser updates or other plugins. If the wallet stops responding, try disabling other extensions first. Sometimes a privacy extension conflicts with the wallet UI. Another trick: clear the site-specific cache for the dapp you’re using. That resets the handshake without nuking everything.
Also: exported keys and migration. If you ever need to export a private key, do it offline and delete any temp files. I know, that sounds paranoid, but keys on the clipboard are a hazard—clipboard malware is real. I keep a disposable machine for exports when I must.
FAQ
Can a browser extension wallet be as secure as a hardware wallet?
Short answer: no, not fully. Extensions are more convenient and more exposed. Hardware wallets add a physical factor that greatly reduces remote compromise risk. That said, you can pair them: use the extension for UI convenience and require the hardware for signing large transactions.
What if I accidentally approve a malicious transaction?
Act fast. If tokens were moved you may be able to trace the destination and reach out to marketplaces or platforms that can freeze assets, though that rarely helps with irreversible transfers. Report the incident to the wallet’s support and keep all evidence. And learn from it—adjust your habit and wallet structure so it won’t recur. I’m not 100% sure every case will resolve, but documenting helps.
I’ll be honest—this part bugs me: people treat wallets like email accounts. They shouldn’t. A wallet is custody. It’s private property. If you stash crypto casually, you increase chances of loss. I’m biased toward a slightly old-school approach: paper backups, hardware wallets, and layered accounts. That approach is fussier, but it scales with the value you hold.
On one hand, browser extensions unlock the full Solana UX and make onboarding friends easy. On the other hand, they require constant attention to permissions and hygiene. Initially I wanted a single-sentence rule to live by, but the reality is more nuanced: adapt your setup to how much value you manage, and be prepared to change the setup as threats evolve. Actually, wait—let me rephrase that: treat your wallet like your front door. Keep the key safe, and don’t let just anyone behind it.
So yeah—try the extension, tweak daily habits, and maybe keep a small sandbox wallet for experiments. It’s not perfect. Nothing is. But with some deliberate steps you can enjoy Solana’s fast chains without handing over your keys to a stranger. Somethin’ about that balance feels right to me, and I hope it helps you get there too.

